I’ve received this morning a private message from a partner pointing me to some Github discussions about resourceExposurePolicy and the possibility to download source code when allowDownloadingSource is set to false.
I think that some threads on the Github repo does not reflect the actual changes and this is why I’ve decided to write this quick post. If you’re new to the resourceExposurePolicy concept, you can read also my old post here.
When developing an extension, your code is by default protected against downloading or debugging of your code. Previous to version 19, these settings where managed by the ShowMyCode property in the app.json file. With Business Central 2021 release wave 2 (version 19), the ShowMyCode setting has been replaced by the resourceExposurePolicy setting which offers a richer access control.
Question raised was: if I have an extension with ShowMyCode = false, my source code download was always protected despite the type of deployment of my app (PTE or Dev scope). Is it the same with the new resourceExposurePolicy?
Some threads on Github points to an initial behaviour, where deploying an extension with the resourceExposurePolicy settings where you set “allowDownloadingSource”: false permits you to download the source code despite the protection if the extension was deployed with the DEV scope (so, from Visual Studio Code).
This was an initial behaviour, planned just because a DEV extension is meant for development (not for deployment!) so all development facilities were enabled. But this was not totally compliant to partner’s IP protection (if you forgot a DEV extension installed on the tenant, someone was able to download the source code) and now the behaviour is different.
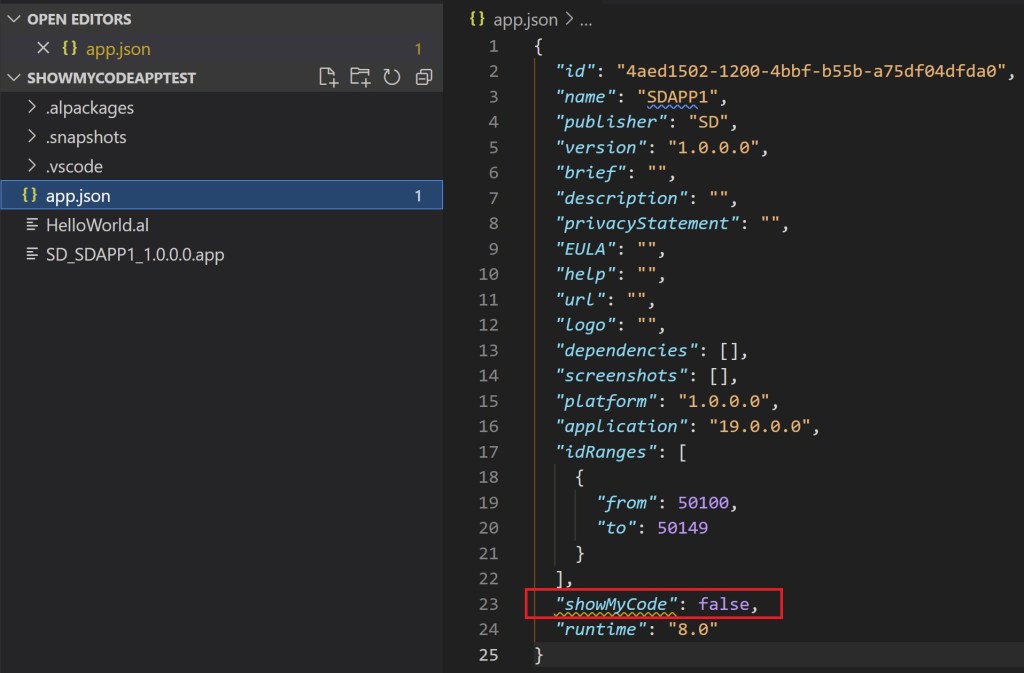
To quickly show that, I’ve created a simple extension (PTE) in two versions, one (here called SDAPP1) were I’ve used ShowMyCode = false (now obsoleted) and one (called SDAPP2) where I’ve used the resourceExposurePolicy. The first app is defined as follows:
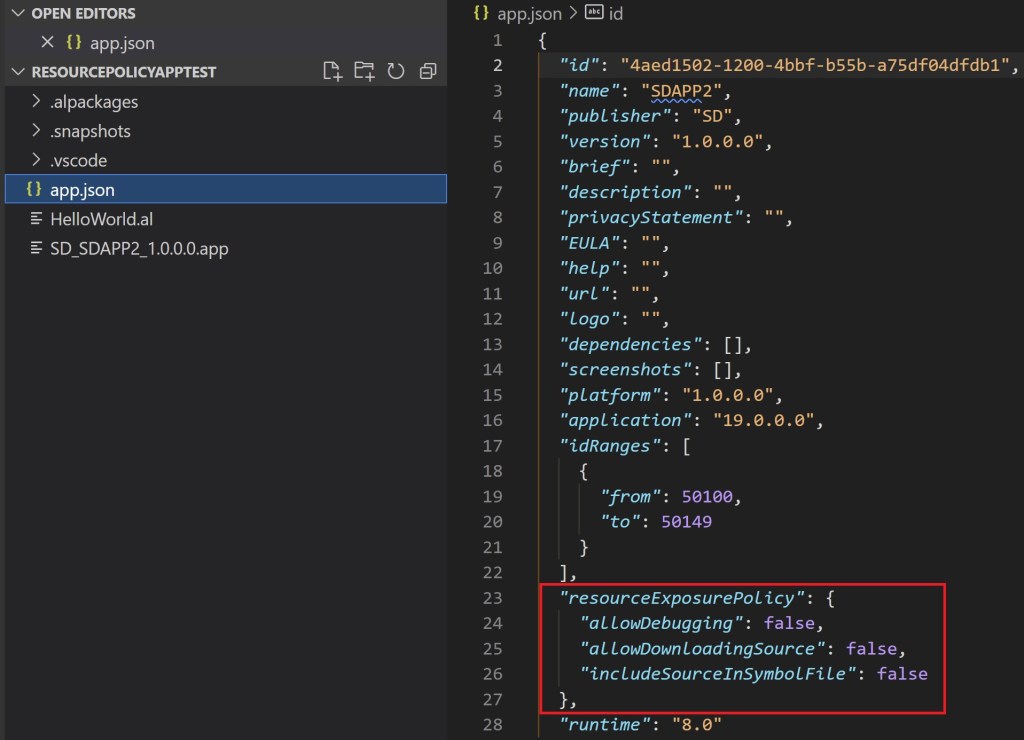
and the second app is defined as follows:
NOTE: please note that with version 19, If ShowMyCode is set, default values for the resourceExposurePolicy will be applied (false).
Now, the goal is to deploy both apps on a SaaS tenant and see if there are differences on behaviour if the app is deployed with a PTE scope or with a DEV scope.
TEST1 – SDAPP1 deployed with PTE scope:
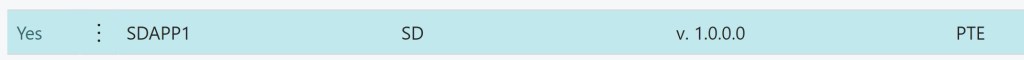
If we select the app from the Extension Management page and we try to download the source, this is the result:
TEST2 – SDAPP1 deployed with DEV scope:

If we try to download the source code:
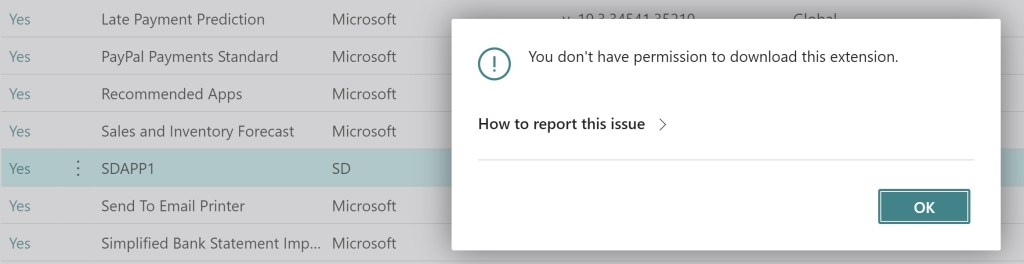
ShowMyCode = false protects the source code downloading on both cases!
Now, let’s test with the app that uses the resourceExposurePolicy settings:
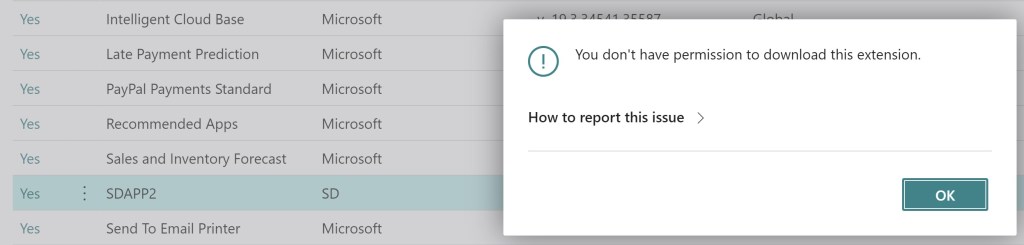
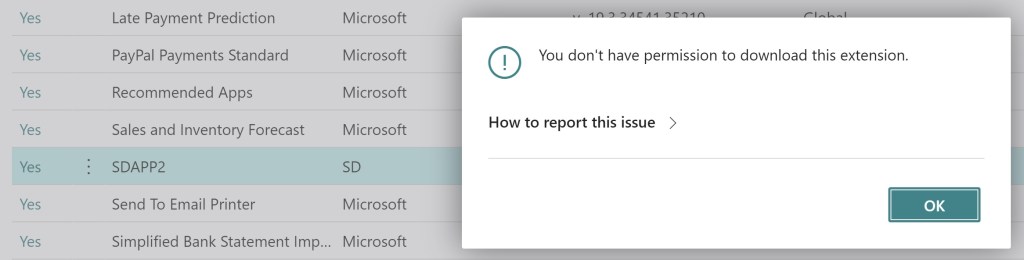
TEST 3 – SDAPP2 deployed with PTE scope:
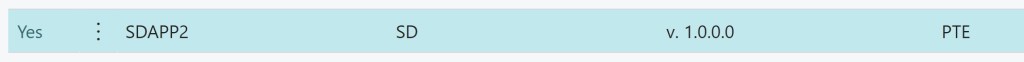
If we try to download the source:
TEST 4 – SDAPP2 deployed with DEV scope:
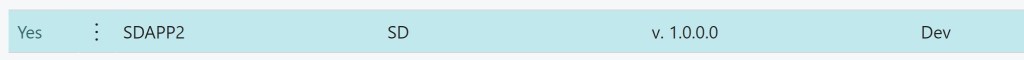
If we try again to download the source code:
Now, also a resourceExposurePolicy with “allowDownloadingSource”: false for a per-tenant extension deployed with the DEV scope blocks the download of the source code.
Obviously, as said before the DEV scope is meant for development and troubleshooting purposes, so if you deploy your extension as DEV scope, the debugging is still allowed despite the policies:
If you want to fully protect your IP, please remember to avoid leaving DEV extensions installed on the tenant (and please also remember that a DEV extension is uninstalled during the tenant upgrade).





What do you mean with “type of deployment” (PTE or Dev scope)? When or how do you do this?
LikeLike
You can deploy an per-tenant extension in two “scopes”:
– PTE scope: extension deployed from extension management page
– DEV scope: extension deployed from Visual Studio Code
LikeLike
Hi Stefano,
I’ve published my own extention forgetting to set allowDownloadingSource to true.
Now the message is : “The effective policies for this package do not allow you to download the source code. Contact the extension provider for more information.”
and I’m not able to change that, ever in second extention version.
Many thanks for your really instructive blog.
Hicham
LikeLike
AllowDownloadingSource can be changed by publishing a new version of the app. When this flag is set to true in the app.json file of extension, the source code and any media files of the extension can be downloaded, for example, from the Download Source option in the Extension Management page in Business Central. The extension can be a PTE or a DEV extension.
LikeLike