In January 2022 Microsoft has released a preview of Granular Delegated Admin Privileges (GDAP) for Microsoft 365 workloads.
Delegated Admins permits to distributors (Microsoft Indirect Providers/CSP Tier 1s) and Microsoft Partners (Indirect Resellers) to manage a customer tenant without using customer licenses (you can provide support and manage administrative tasks on the tenant).
Delegated Admins Privileges (DAP) are widely used for administering Dynamics 365 Business Central tenants (and it’s recommended to use them) but they have a possible drawback: they can give you access as Global Admin to your customer tenants and so if you are compromised (alias hacked) also your customers could be affected.
The new GDAP capability will allow partners to control more granular and time-bound access to their customers’ workloads, to better address their customers’ security concerns. Partners can also offer more services to customers who may be uncomfortable with the current levels of partner access or those who have regulatory requirements to provide only least-privileged access to partners.
With DAP, you can have the following two access roles:
- Global Admin
- HelpDesk Agent
and the relationship timeline is indefinite (it lives until the customer revoke it). The customer needs to accept the relationship via a link that is the same for every customer.
With GDAP you can set-up custom access roles with custom relationship timelines (maximum of 2 years, after that it must be renewed) by accepting a relationship from a customer-specific link. All GDAP related operations are logged into the Azure AD Activity logs for traceability.
With DAP, the same level of access is given to all members within a Partner Center environment for a specific customer, while with GDAP you can create security groups with specific roles.
Please take into consideration that GDAP will replace DAP in the near future.
How to set-up a GDAP relationship with a Customer
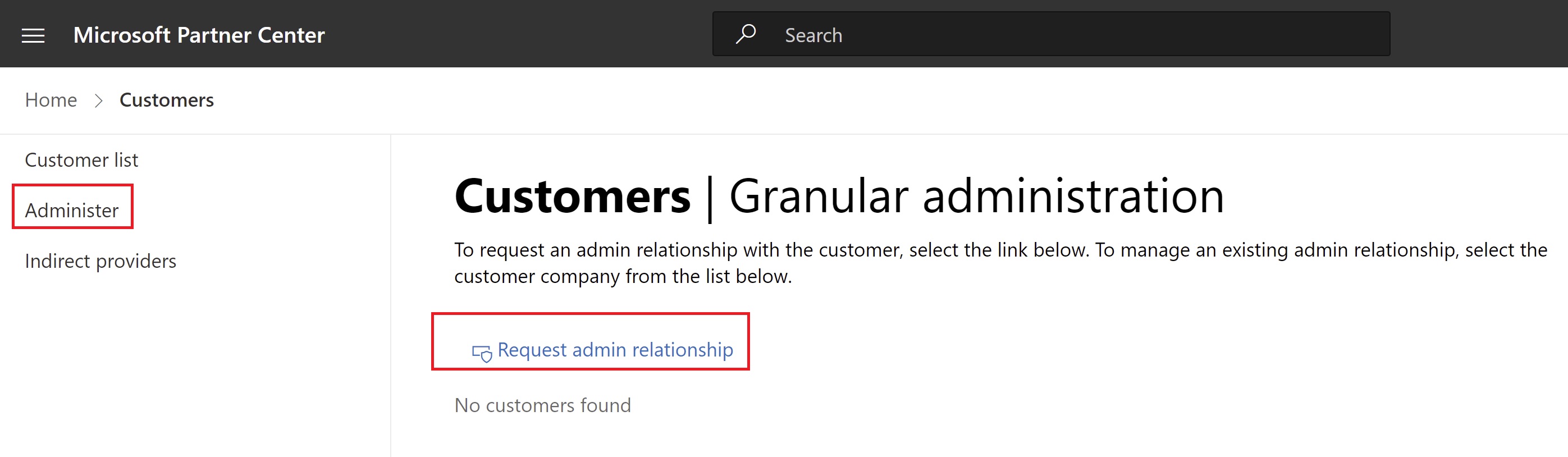
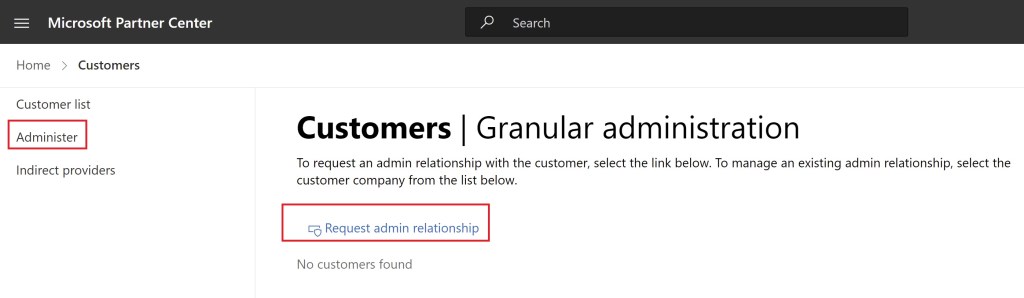
To set-up a Granular Delegated Admin relationship with a Customer, you need to access your Partner Center account and select the Customers section. Here click on Administer and then on Request admin relationship:
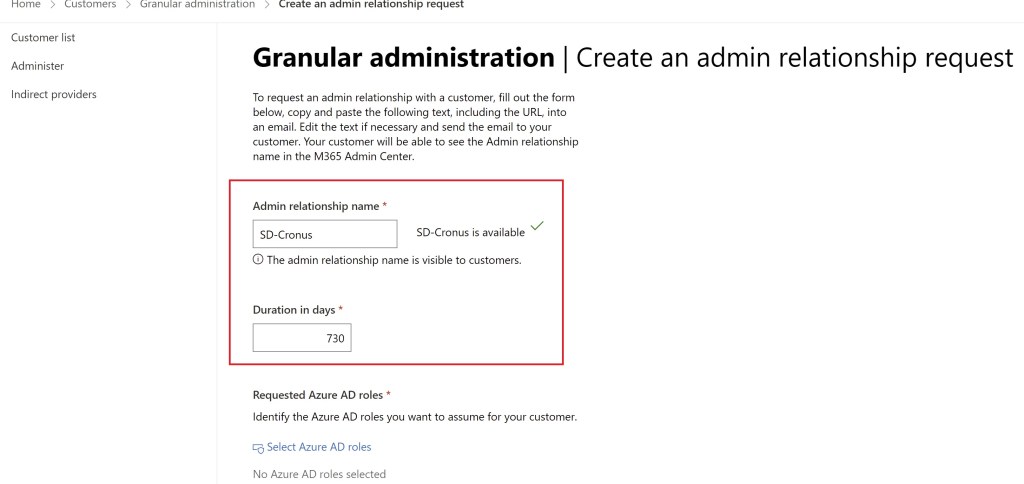
Here you need to provide an Admin relationship name that must be unique in your tenant and the duration can be maximum 730 days (2 years) but you can obviously restrict it accordingly to your contract:
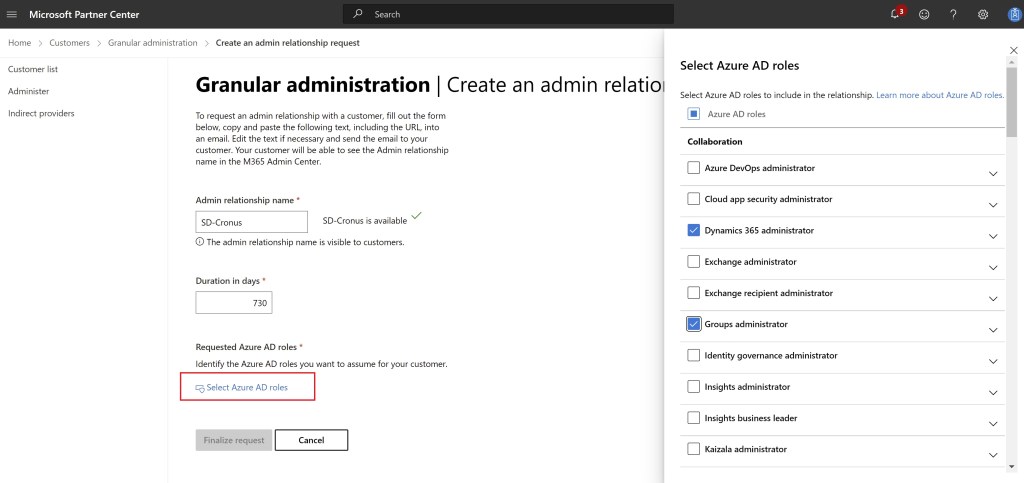
Then click on Select Azure AD roles. Here is where you can set-up the Azure AD roles to include in your GDAP relationship with this customer:
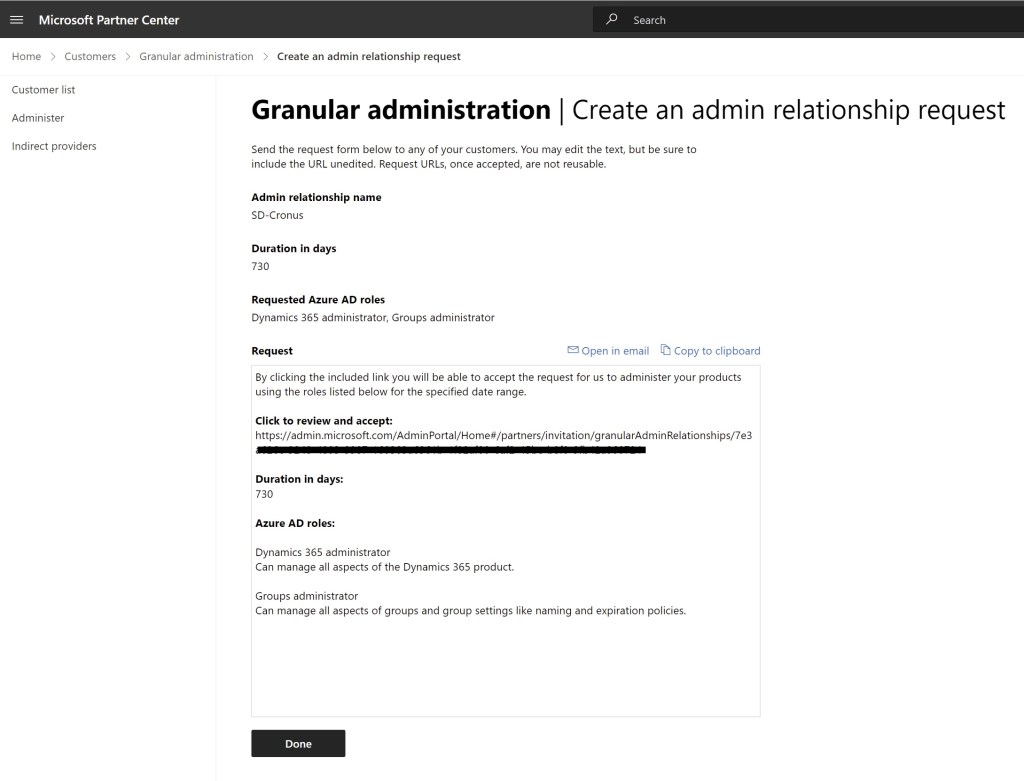
When the needed roles are selected, you can click on Save (at the bottom of the roles list) and then on Finalize request:
You can then send this email to your customer in order to establish the relationship.
When your customer receives the email, it must click on the above link with a Global Admin account in order to accept the relationship.
When the relationship is accepted, the customer will see the new relationship in the Partner Relationships section for its customer tenant (marked as Granular admin access).
This is not the end of the process however!
When the relationship is established, in your Partner Center account you need to select your customer, click on Admin Relationship and view the existing GDAP configuration.
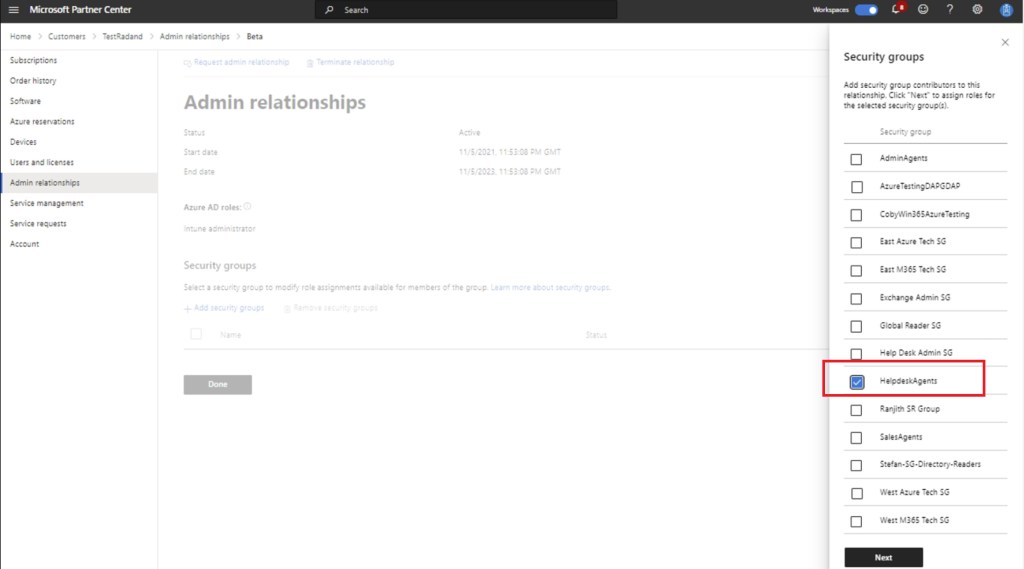
Here you can select your established GDAP relationship and click on Add Security Group for modifying the role assignments available for the members:
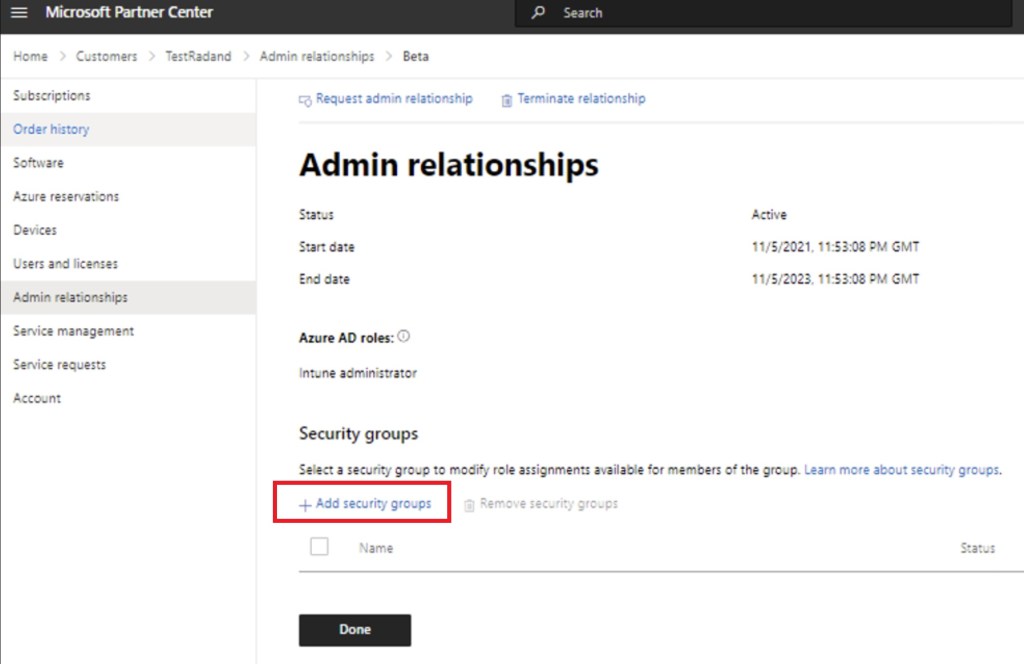
this is where you can select the security groups that you want to grant permissions to the GDAP relationship (fo example, the HelpdeskAgents group):
Select Save and the security group now appears in the Security groups section.
Now select the newly added security group and the Select Azure AD roles side panel opens. Now you can choose the Azure AD roles you want to assign to the security group for that admin relationship. The Azure AD roles assigned will enable the users in the security group to administer services:

Please consider the following before start using this new feature:
- GDAP takes precedence over DAP on a customer tenant, so be careful on setting permissions.
- Microsoft has plans to provide an “automatic way” of moving from DAP to GDAP for existing relationships, without forcing partners to re-send relationship requests again. No ETA for this yet.
- The granular delegated admin privileges (GDAP) relationship will automatically expire when the duration requested in the invitation is passed. Before expiration, you will receive proactive email notifications 30 days, seven days, and one day before the GDAP expiration date.
- Partners can see details of their expired relationships in the Admin relationships section within Partner Center.
- To extend or renew the GDAP relationship, partners will need to resend the GDAP relationship request to the customer (auto-renewal process is not supported for security reasons).
- There will be available APIs for automating the GDAP relationship creation process with customers.
- You can view your granular delegated admin privileges (GDAP) relationship activity on the activity log page in your Partner Center account settings and also export them as .csv file.
- GDAP and DAP coexists now, but in the future you will be required to have a GDAP relationship with any customers you wish to administer services to.
- GDAP works for Microsoft 365 and Dynamics 365 workloads. Azure is not in scope yet for GDAP.
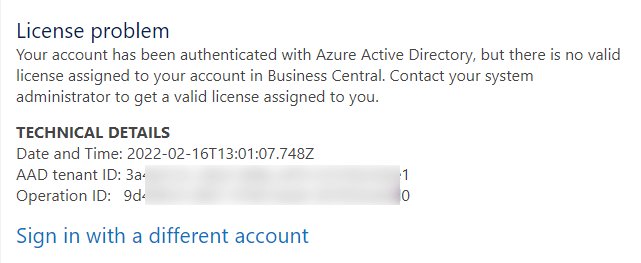
NOTE: if your users are registered in the customer’s Azure AD as Guest users (maybe because they were invited to join the organization on Teams) you could have the following error:
"Your account has been authenticated with Azure Active Directory, but there is no valid license assigned to your account in Business Central."
This is actually by-design. You can either be setup as a guest in the customer’s AAD and then having assigned a valid Business Central license, or you can use the Delegated Admin auth flow. You cannot do both.


Hi Stefano,
I just performed this procedure for one of our new customers.
It works very well.
I just had a question:
Do you know why the user created in BC corresponding to my login account is formatted like this:
user_000XXX000X0X0000X00XXX000XX0XXX0
Thanks a lot.
LikeLike
Hi Stefano,
I found the answer to my previous question here:
https://docs.microsoft.com/en-us/dynamics365/business-central/dev-itpro/administration/delegated-admin
But,
Do you know why I can’t setup the new feature Email Logging using Graph ?
Error:
Your license does not grant you the following permissions on TableData Email Logging Setup: Insert.
And,
The same for accessing to effective permissions ?
Error:
The effective permissions content can be shown only for Azure AAD users.
Should the Email Logging setting be done by a user of the Azure AD tenant ?
Or should I request additional Azure AD roles in addition to “Dynamics 365 Administrator” for GDAP ?
Thanks a lot.
LikeLike
Not all operations can be done by a delegated admin, this is by design. The owner is the customer on SaaS, for some operations you need a lice se assigned (so real user).
LikeLike
Hi Stefano,
Are you familiar with problems ordering licenses when using GDAP?
It seems I´m not allowed to add a subscription..
LikeLike
Can you please explain the problem? GDAP and selling licenses are not so much related…
LikeLike