Last week at Directions EMEA I had the pleasure to meet and talk with many of you in person and it was nice. Thanks for your kind words and I apologize for those who had asked to have a meeting with me but due to lack of time and sessions overlapping we were unable to arrange it. Feel free to send me a message if needed.
During these “unofficial talks” I’ve received a lot of questions and I’ve promised to answer some of them with more details in the next days with some posts.
One of the questions was related to the new resource exposure policy introduced with Dynamics 365 Business Central 2021 Wave 2 (version 19). I’ve talked about this topic about two months ago here. To summarize my previous post, started from Business Central version 19 in the app.json file you can specify a setting called resourceExposurePolicy that defines the accessibility of the resources and source code during different operations. This new parameter permits you to specify the following options: allowDebugging, allowDownloadingSource, and includeSourceInSymbolFile. Each of these properties define the specific areas in which the source code of an extension can be accessed. These parameters are set to false by default, which means that no dependent extension can debug or download the source code of your extension. You can then change it as needed.
In a session related to debugging extensions, when talking about this new feature (that replaces the ShowMyCode parameter) Microsoft said that you can also change this values for a specific tenant, but no details about this was given and someone asked me for more details.
If I have a resource exposure policy setted for a particular extension in its app.json file, how can I change it for a specific tenant? Is this possible? This could be helpful maybe for temporarily enablig debugging of an extension for a particular tenant.
The answer is YES, it’s possible. You can override the resource exposure policy for an extension for a particular tenant but this requires some steps.
The first step to do is to create an Azure KeyVault instance and then add it to your extension. I’ve talked about how to create and use an Azure Key Vault in an AL extension here.
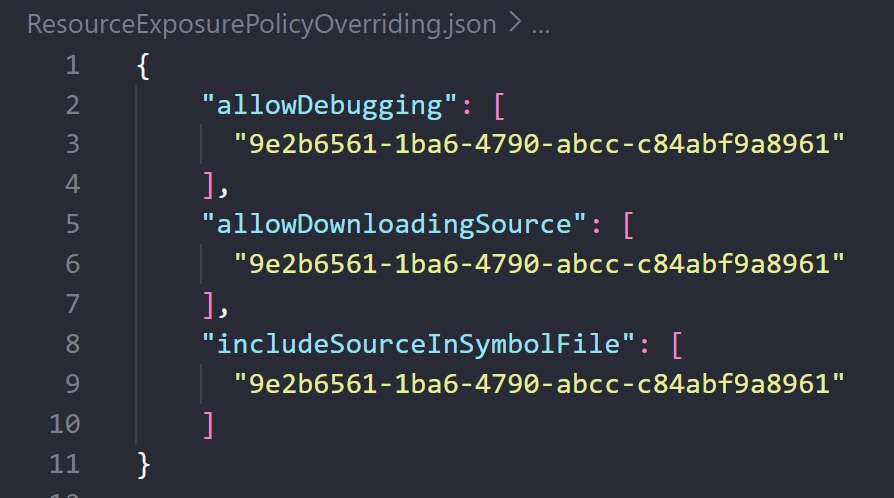
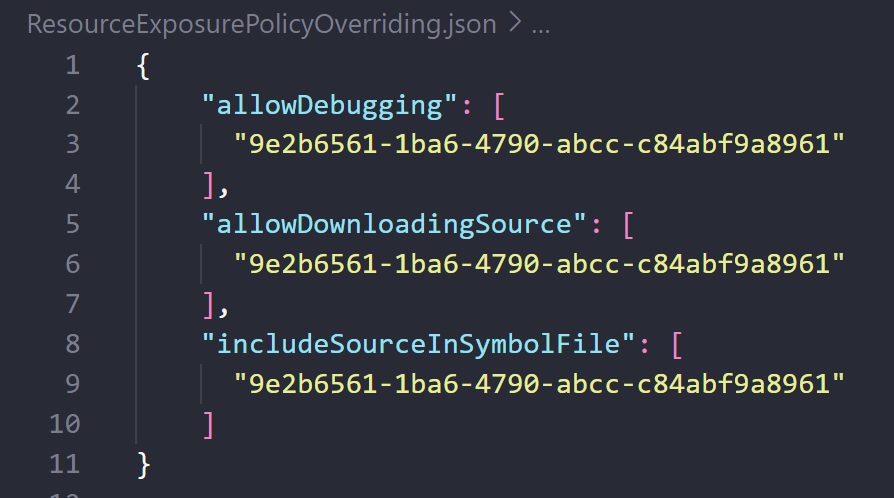
In your Azure Key Vault instance, you need to create a secret called BC-ResourceExposurePolicy-Overrides and the content of this secret must be a JSON like the following:
In the above JSON, for each resource exposure policy parameters (allowDebugging, allowDownloadingSource, and includeSourceInSymbolFile) you can specify an array of tenant IDs for which the relative policy will be enabled.
Adding a JSON value to an Azure Key Vault secret cannot be done directly via the Azure Portal (multi-line secrets are not supported), so you can use Azure Powershell for this:
$json = '{
"allowDebugging": [
"9e2b6561-1ba6-4790-abcc-c84abf9a8961"
],
"allowDownloadingSource": [
"9e2b6561-1ba6-4790-abcc-c84abf9a8961"
],
"includeSourceInSymbolFile": [
"9e2b6561-1ba6-4790-abcc-c84abf9a8961"
]
}'
$Secret = ConvertTo-SecureString -String $json -AsPlainText -Force
Set-AzKeyVaultSecret -VaultName "YourKeyVaultName" -Name "BC-ResourceExposurePolicy-Overrides" -SecretValue $Secret
Then you need to enable your app to read secrets from that Azure Key Vault instance. For this, I suggest to follow these steps.
Please remember that with Dynamics 365 Business Central online, App key vaults can only be used with AppSource apps. They’re not supported with per-tenant extensions (for PTEs it’s not required to override a resource policy because you can always enable debugging for a particular instance).
What happens if the above steps are performed?
Imagine to have an extension called MYAPP published on AppSource that has allowDebugging, allowDownloadingSource, and includeSourceInSymbolFile setted as FALSE (default) in its app.json file. This means that debugging is not allowed on every tenant where your app is installed.
Now imagine to have a critical problem on tenant 9e2b6561-1ba6-4790-abcc-c84abf9a8961. You can publish the above explained secret and ONLY for this tenant the extension MYAPP will have debugging enabled. You can then debug, do your troubleshooting work and then, when finished, you can remove the secret value and your extension will have again the default resource exposure policy (as in the original app.json file).
NOTE: Partner must be delegated admin in order to debug the app in that tenant. At the time of writing this post, snapshots and profiling does not support these dynamic grants.
Please also remember that if you have an Aplication Insights connection string in your app.json file (applicationInsightsConnectionString property) you will have a telemetry signal sent every time a resource policy overriding is read from your Azure Key Vault instance (so you can discover issues on reading the secret).
In this way, debugging AppSource apps could be more flexible… 🙂


Thanks Stafeno. Make this feature more clear for me.
There is one more question need your help. In one of topic, you mentioned about mystery for library app. And we are planning to use that feature, but I cannot find any document regarding how to register a library app with Microsoft and how to get library app object ID range from Microsoft. I am very appreciate if you have any information that can share with me.
Thanks
Tom
Open Door Technology
Canada
LikeLike
A library app has the same steps as a standard AppSource app, so you need to request for a range, use a prefix and then pass validation. Object ids must be requested via your Partner’s channel. Submission of a library app for validation must be done together with an AppSource app. Then, when approved, all your apps that uses this library will receive the update.
LikeLike
Thank you for the quick reply. That help us a lot. Very appreciate. We will start this process now.
LikeLike
Hi Stafeno,
Want to know your opinion about topic for this blog. If we have multiple apps, should we have separate key vault per app or can we share one key vault for all apps? Or Key Vault value will only work with registered app.
For example, we have library app is base for our other apps, can we just have one key vault setting in library app, so we can temporary debug every apps install in customer environment, or we have to have separate key vault each app, and turn this on for each app.
Hope my question make sense.
Thanks
Tom
LikeLike
You can absolutely have a single key vault instance for all your apps. Just remember that in this case this means that the overriding setting described in this post will be valid for all the apps that uses this key vault.
LikeLike